|
WMAP (Metasploit Module)
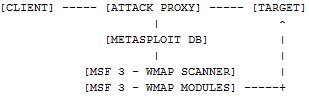
WMAP is a general purpose web application scanning framework recently incorporated into Metasploit 3. In the WMAP design, the attack proxy acts as a data gathering tool. All traffic between the client(s) (i.e. favourite browser and/or spider) will be stored in the MSF database.
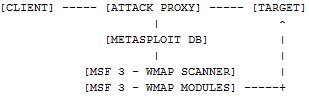
WMAP is a Metasploit plugin and interacts with the database, reading all gathered traffic, processing it and launching the different tests implemented as modules. As WMAP Modules are MSF Modules they can be easily implemented, and can be run manually from the command line or automatically via WMAP. At the time of writing WMAP can use/ initiate the following (ruby) modules to conduct its test against the target website (I'm sure more will be forthcoming in the near future :-) ).
| | | | | | | - wmap_prev_dir_same_name_file
| | | | | | | |
A detailed explanation of WMAP can be found here
Requirements
Metasploit :-) Ratproxy SQLite3
Note: - Metasploit requires the following packages: ruby ruby-irb ruby-libs ruby-rdoc ruby-devel readline rubygems Installation Ratproxy [root@FC9 ~]# wget http://ratproxy.googlecode.com/files/ratproxy-1.51.tar.gz
--2008-11-27 19:17:13-- http://ratproxy.googlecode.com/files/ratproxy-1.51.tar.gz
Resolving ratproxy.googlecode.com... 74.125.47.82
Connecting to ratproxy.googlecode.com|74.125.47.82|:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 168409 (164K) [application/x-gzip]
Saving to: `ratproxy-1.51.tar.gz'
100%[======================================>] 168,409 54.2K/s in 3.0s
2008-11-27 19:17:16 (54.2 KB/s) - `ratproxy-1.51.tar.gz' saved [168409/168409]
[root@FC9]# tar -zxvf ratproxy-1.51.tar.gz Now we need to patch ratproxy with the supplied patch in metasploit:
[root@FC9 ratproxy]# patch -d . < /framework-3.2/external/ratproxy/ratproxy_wmap.diff
patching file Makefile
patching file ratproxy.c
patching file http.c
[root@FC9 ratproxy]# make [DONE]
SQLite 3 [root@FC9]yum install sqlite3 We also need sqlite3-ruby which I installed from within metasploit msfconsole itself msf > gem install sqlite3-ruby
[*] exec: gem install sqlite3-ruby
Building native extensions. This could take a while...
Successfully installed sqlite3-ruby-1.2.4
1 gem installed
Installing ri documentation for sqlite3-ruby-1.2.4...
Installing RDoc documentation for sqlite3-ruby-1.2.4... Execution: Load the databases and create a wmap testing database ./msfconsole msf > load db_sqlite3
[*] Successfully loaded plugin: db_sqlite3
msf > db_create wmapper.db
[*] Creating a new database instance...
[*] Successfully connected to the database
[*] File: wmapper.db
msf > load db_wmap
[*] =[ WMAP v0.3 - ET LoWNOISE
[*] Successfully loaded plugin: db_wmap
msf > db_connect wmapper.db
[*] Successfully connected to the database
[*] File: wmapper.db Start Ratproxy: [root@FC9 ratproxy]# ./ratproxy -v /framework-3.2/ -b wmapper.db
ratproxy version 1.51-beta by <lcamtuf@google.com>
[!] WARNING: Running with no 'friendly' domains specified. Many cross-domain
checks will not work. Please consult the documentation for advice.
[*] Proxy configured successfully. Have fun, and please do not be evil.
[+] Accepting connections on port 8080/tcp (local only)...
Change your proxy settings in Firefox to use port 8080
Browse to target website msf > wmap_targets
[*] Usage: wmap_targets [options]
-h Display this help text
-p Print all available targets
-r Reload targets table
-s [id] Select target for testing
msf > wmap_targets -r
[*] Added. 107.86.156.139 80 0 [*] Added. 107.86.156.142 80 0
msf > wmap_targets -p
[*] Id. Host Port SSL
[*] 1. 107.86.156.139 80 [*] 2. 107.86.156.142 80
[*] Done.
Select the instance you wish to test against (in this case instance 1) msf > wmap_targets -s 1 Set the tool to quickly review the websites structure
msf > wmap_website
[*] Website structure
[*] 107.86.156.139:80 SSL:0
ROOT_TREE
| styles
| +------style2.css
[*] Done.
Load any available modules msf > wmap_run -t
[*] Loaded auxiliary/scanner/http/frontpage ...
[*] Loaded auxiliary/scanner/http/frontpage_login ...
[*] Loaded auxiliary/scanner/http/wmap_vhost_scanner ...
[*] Loaded auxiliary/scanner/http/version ...
[*] Loaded auxiliary/scanner/http/wmap_ssl_vhost ...
[*] Loaded auxiliary/scanner/http/wmap_prev_dir_same_name_file ...
[*] Loaded auxiliary/scanner/http/wmap_files_dir ...
[*] Loaded auxiliary/scanner/http/wmap_dir_listing ...
[*] Loaded auxiliary/scanner/http/wmap_replace_ext ...
[*] Loaded auxiliary/scanner/http/wmap_brute_dirs ...
[*] Loaded auxiliary/scanner/http/wmap_file_same_name_dir ...
[*] Loaded auxiliary/scanner/http/writable ...
[*] Loaded auxiliary/scanner/http/wmap_dir_scanner ...
[*] Loaded auxiliary/scanner/http/wmap_backup_file ...
[*] Loaded auxiliary/scanner/http/wmap_blind_sql_query ...
[*] Analysis completed in 2.4388530254364 seconds.
[*] Done.
Run the available modules msf > wmap_run -e
[*] Launching auxiliary/scanner/http/frontpage WMAP_SERVER against 107.86.156.139:80
[*] http://107.86.156.139:80 is running Microsoft-IIS/6.0
[*] FrontPage not found on http://107.86.156.139:80 [404 Not Found]
[*] Launching auxiliary/scanner/http/frontpage_login WMAP_SERVER against 107.86.156.139:80
[*] http://107.86.156.139:80/ may not support FrontPage Server Extensions
[*] Launching auxiliary/scanner/http/wmap_vhost_scanner WMAP_SERVER against 107.86.156.139:80
[*] Launching auxiliary/scanner/http/version WMAP_SERVER against 107.86.156.139:80
[*] 107.86.156.139 is running Microsoft-IIS/6.0 ( Powered by ASP.NET )
[*] Launching auxiliary/scanner/http/wmap_ssl_vhost WMAP_SERVER against 107.86.156.139:80
[*] Error: 107.86.156.139 unknown protocol
[*] Launching auxiliary/scanner/http/wmap_prev_dir_same_name_file WMAP_DIR / against 107.86.156.139:80...
[-] Blank or default PATH set.
[*] Launching auxiliary/scanner/http/wmap_prev_dir_same_name_file WMAP_DIR /styles/ against 107.86.156.139:80
[*] NOT Found http://107.86.156.139:80/styles.null
[*] NOT Found http://107.86.156.139:80/styles.backup
--------- ABRIDGED --------------
[*] Launching auxiliary/scanner/http/wmap_backup_file WMAP_FILE /styles/style2.css against 107.86.156.139:80
[*] NOT Found http://107.86.156.139:80/styles/style2.css.backup
[*] NOT Found http://107.86.156.139:80/styles/style2.css.bak
[*] NOT Found http://107.86.156.139:80/styles/style2.css.copy
[*] NOT Found http://107.86.156.139:80/styles/style2.css.old
[*] NOT Found http://107.86.156.139:80/styles/style2.css.orig
[*] NOT Found http://107.86.156.139:80/styles/style2.css.temp
[*] NOT Found http://107.86.156.139:80/styles/style2.css.txt
[*] NOT Found http://107.86.156.139:80/styles/style2.css~
[*] NOT Found http://107.86.156.139:80/styles/.style2.css.swp
What are the reporting options:
msf > wmap_reports
[*] Usage: wmap_reports [options]
-h Display this help text
-p Print all available reports
-s [id] Select report for display
Display all available reports
msf > wmap_reports -p
[*] Id. Created Target (host,port,ssl)
1. Thu Nov 27 20:34:28 +0000 2008 107.86.156.139,80,0
[*] Done.
Select instance 1 msf > wmap_reports -s 1
WMAP REPORT: 107.86.156.139,80,0 Metasploit WMAP Report [Thu Nov 27 20:34:28 +0000 2008]
WEB_SERVER TYPE: Microsoft-IIS/6.0 ( Powered by ASP.NET ) [Thu Nov 27 20:34:31 +0000 2008]
DIRECTORY NAME: /News/ Directory /News/ found. [Thu Nov 27 20:49:07 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:49:07 +0000 2008]
DIRECTORY NAME: /contact/ Directory /contact/ found. [Thu Nov 27 20:50:26 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:50:27 +0000 2008]
DIRECTORY NAME: /faq/ Directory /faq/ found. [Thu Nov 27 20:51:08 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:51:08 +0000 2008]
DIRECTORY NAME: /forum/ Directory /forum/ found. [Thu Nov 27 20:51:16 +0000 2008]
DIRECTORY RESP_CODE: 200 [Thu Nov 27 20:51:16 +0000 2008]
DIRECTORY NAME: /images/ Directory /images/ found. [Thu Nov 27 20:51:37 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:51:37 +0000 2008]
DIRECTORY NAME: /resources/ Directory /resources/ found. [Thu Nov 27 20:53:00 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:53:00 +0000 2008]
DIRECTORY NAME: /services/ Directory /services/ found. [Thu Nov 27 20:53:12 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:53:12 +0000 2008]
DIRECTORY NAME: /styles/ Directory /styles/ found. [Thu Nov 27 20:53:37 +0000 2008]
DIRECTORY RESP_CODE: 403 [Thu Nov 27 20:53:37 +0000 2008]
[*] Done.
msf >
Okay nothing startling from the test server but then I new it wasn't vulnerable before I tested it :-)
References: These I found very useful, I had a few gotchas on my default install, especially with sqlite3-ruby not being installed which made my life fun till I sorted that one out :-(
http://darkoperator.blogspot.com/2008/10/metasploit-wmap-web-attack-and.html
http://carnal0wnage.blogspot.com/2008/11/metasploit-and-wmap_24.html
http://code.google.com/p/ratproxy/wiki/RatproxyDoc Code:
Ratproxy is available from http://code.google.com/p/ratproxy/
|