|
 |
 |
 |
 |
  |
|||
 |
 |
 |
|
|
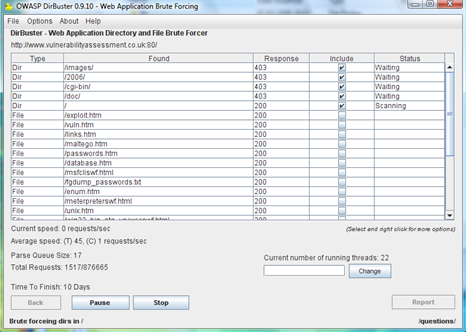
DirBuster
OWASP's DirBuster is a multi threaded (OS independant) java application designed to brute force directories and files names on web/application servers. Often is the case now of what looks like a web server in a state of default installation is actually not, and has pages and applications hidden within. DirBuster attempts to find these. However tools of this nature are often as only good as the directory and file list they come with. A different approach was taken to generating these. The list was generated from scratch, by crawling the Internet and collecting the directory and files that are actually used by developers!
DirBuster comes with a total of 9 different lists which makes DirBuster extremely effective at finding those hidden files and directories. And if that was not enough DirBuster also has the option to perform a pure brute force, which leaves the hidden directories and files nowhere to hide! (Although this is time consuming).
It is available from here.
Requirements:
Installation and Execution:
Unzip/ untar the download change to DirBuster directory Windows - Double-click on the DirBuster jar file Unix - java -jar DirBuster-0.9.10.jar Pre-requisites
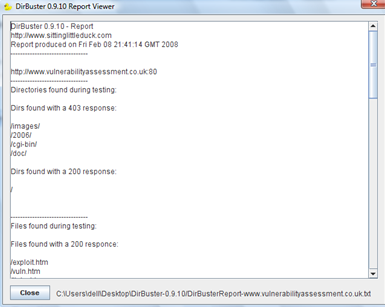
After completion the following example report can be generated:
|
IT Security News:
Pen Testing Framework:
Latest Tool Reviews:
|
| © VulnerabilityAssessment.co.uk 25 February 2008 |
|