|
 |
 |
 |
 |
  |
|||
 |
 |
 |
|
|
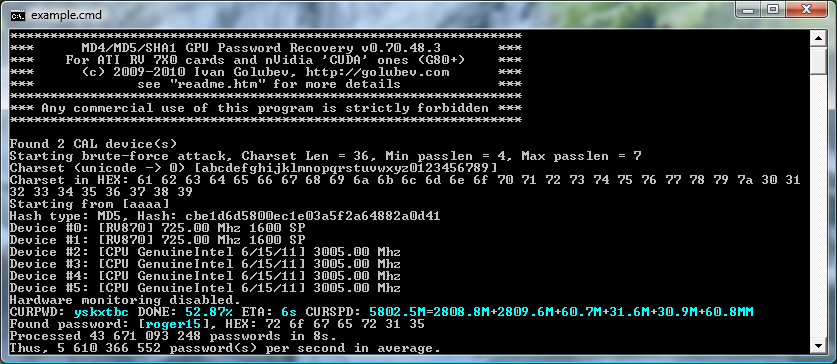
Ighashpu
Ighashpu is a program to recover/crack SHA1, MD5 & MD4 hashes.
As ighashgpu supports salted hashes it's possible to use it for:
Supported Cards/ Requirements
Current statusIt is available from here UsageSyntax ighashgpu.exe [switch:param] [hashfile.txt] Note:- hashfile.txt only used with unsalted MD5 hashes. This file must contain plain MD5 hashes (32 HEX digits - username:hash) or simply hash at each line. For example: aaaa:74b87337454200d4d33f80c4663dc5e5 aaab:4c189b020ceb022e0ecc42482802e2b8 -c csdepa Charset definition (caps, smalls (default), digits, special, space, all) -u [chars] User-defined characters -uh [HEX] User-defined characters in HEX (2 chars each) -uhh [HEX] User-defined characters in Unicode HEX (4 chars each) -uf [filename] Load characters from file. Not used with Unicode. -sf [password] Password to start attack from -m [mask] Password mask -ms [symbol] Mask symbol -salt [hex] Append salt after password -asalt [string] Append salt in ascii after password -usalt [string] Append salt in unicode after password -ulsalt [string] Same as above but unicode string firstly transformed to lower case -min [value] Minimum length (default == 4), must be >= 4 -max [value] Maximum length (default == 6), must be <= 31 (not counting salt length) -h [hash] Hash to attack (16 or 20 bytes in HEX) -t [type] Type of hash to attack
-devicemask:[N] Bit mask for GPUs usage, bit 0 == first GPU (default 0xFF, i.e. all GPUs).
Note: - Special parameters (like " or /) can be passed by using single or double quotes: -asalt "h/X" -cpudontcare Tell ighashgpu that you want maximum from GPU and so don't care about CPU usage at all (and it means one CPU core at 100% per one GPU). -hm [N] Set threshold temperature for hardware monitoring, default is 90C. You can disable monitoring by setting this value to zero. -blocksize [N] Set block size, by default N = 23 which means 2^23 = 8388608 passwords offloaded to GPU in a single batch. By default charset processed as ANSI one. (i.e. WideCharToMultiByte(CP_ACP, ...) You can change this with: -unicode Use unicode |
IT Security News: more........
Pen Testing Framework:
Information:
|
| © VulnerabilityAssessment.co.uk 16 May 2010 |
|